The Pentagon has teamed up with DARPA and other agencies to create a “self-aware” AI, robot, that will use posts on social media to decipher a threat level of an individual and determine whether or not they should be placed on a kill list.
It’s called “Thrust”, a new initiative from the Pentagon that will use predictive social media algorithms to determine when to use lethal force. Under Jade Helm 15, a new era began, the era of artificial intelligence and predictive technologies that “map the human domain”. And now just a year later, this field is greatly expanding.
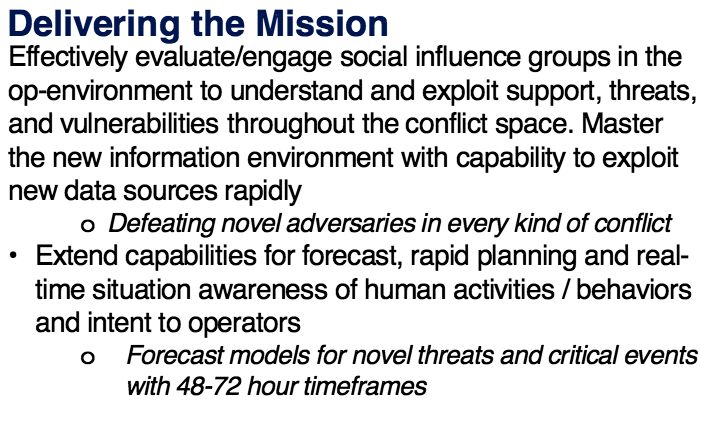
Admitted in the document is the use of governmental shills, designed to infiltrate social media groups such as on Facebook, Twitter or Google, and then take an analysis of sorts. Within 48-72 hours, the AI shill will have analyzed, understood, and found a way to exploit support, threats and vulnerabilities based on an individual’s behavior and activities.
[easy-tweet tweet=”Analyze this AI; Project Thrust Exposed, Killer robot to Analyze Social Media Posts…” hashtags=”ai, artificialintelligence, ” url=”###”]
Through advanced cognitive analysis, human personality, traits, weaknesses will be quickly uncovered all through the voluntary process of the target sharing their personal life on social media platforms.
In the old days, to analyze a “threat” the government would need to deploy an agent to get close to the supposed threat and report back. Not so anymore, with Facebook and the like the “threat” will do all the work for them, providing real time updates on the latest personal details to be analyzed, and ultimately exploited through predictive technology.
The Program overview:
- Crisis and Disaster Informatics and Models
- Social Network Research on New Threats(Daesh, Novorossiya)
- Text Analytics for Context and Event Prediction
- Foreign Language Machine Translation for Threat Warnings
- COI
-coordinated SBIR projects for full spectrum social media analysis
The “human domain” will be exploited and infiltrated using artificial intelligence to extract delicate information from social data. The Pentagon’s attempts at creating an AI for social media analysis is not a new one; rather it has been done in the past during massive exercises. For example, NATO’s large military function called Trident Junction 2015, was the first attempt at extracting social media analysis. According to the declassified 2016 Department of Defense (DoD) document, the Human Systems Roadmap Review, Trident Junction was a success.
Recall Jade Helm 15? Freedom Fighter Times issued a warning that it was about our reactions to the mass drills ongoing throughout the US, uncovered was the documentation to prove that the military was working on predictive technologies that would analyze our behaviors. Now, a year later the classified document, confirms that predictive technologies, and social media analysis is what was going on, and what is advancing in the future.
[fvplayer src=”https://www.youtube.com/watch?v=VGJNBqgSAqU” splash=”https://christianjournal.net/wp-content/uploads/2016/06/pentagon-research-projects.jpg”]
The perturbing point about the entire operation is that we the people are their experiments. The analysis of data done by algorithms and artificial intelligence will not get conducted on just those suspected of “terrorism,” but rather the Pentagon will do it on a mass scale. Countless unsuspecting individuals have their personal files captured by the NSA analyzed, and their threat level to the US government deciphered.
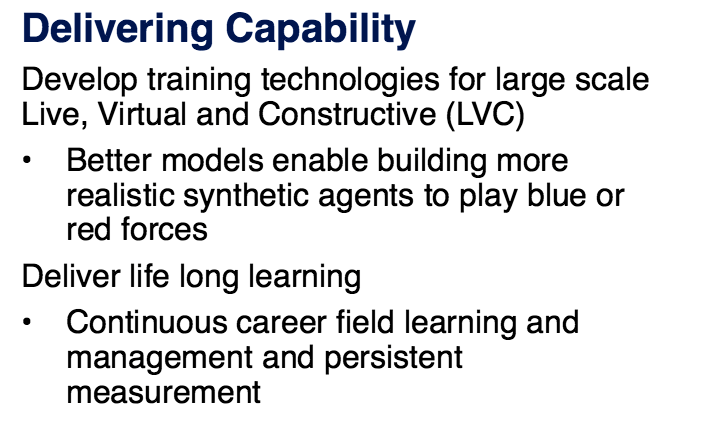
In Human Systems Roadmap Review, blue and red forces are brought up in reference to the simulations used in training the armed forces to use this technology (see image below). Within the simulation, the red and blue agents would be the targets. The government has created a red and blue list to categorize who is and isn’t a threat. The red and blue list became a well-known phenomenon relating to martial law as citizens across the country discovered red or blue markings on their curbs and mailboxes. Around the same time, information was leaked that the red list was marked for extermination as they were a high threat and blue was marked for FEMA and brainwashing as their threat level was low, and they could be easily manipulated.
Under this new program, the main point of capture is through social media groups. The Human Systems Roadmap review, brought about by Dr. John Tangney, SES Director, Human and Bioengineered Systems Division, ONR Chair, Human Systems Community of Interest, is all about biotechnology. The data capture is the first step in implementing the Mark of the Beast Technology. For one simple reason, knowing all of an individual’s information is not enough, because there are wild cards; which means that the government will attempt to implement a “thought tracking” technology as well. Whether or not that is considered Sci-Fi, it is proving to be true. DARPA is working on what is called a BCI, brain-computer interface, or in other words a brain modem, which will transmit data from your brain back to connected devices. All controlled by thoughts rather than limbs.
Welcome to the New World. Technology is the future of mankind, and it truly means the end of personal liberties all lining up with prophecy. All that is listed above is the beginning steps in implementing their control of society, which FFT uncovered in our Unlimited section regarding Martial Law, Biotechnology, and the GMO link to Mind Control; FFT uncovered information like this and so much more.
The documents which now are available publicly were made public for one reason; their system is already up and running. See official declassified document below; which you can also download by clicking on the download link below.
[embeddoc url=”https://www.dropbox.com/s/nq0a85r8glsc8oq/NDIA_Human_Systems_Conference_2016_HSCOI_DistroA_FINAL.pdf?dl=1″ download=”all” viewer=”google”]
Co-Author: Emma Noelle




![[VIDEO] Drag Queen Drag Shows Are Now Infesting Churches](https://christianjournal.net/wp-content/uploads/2019/11/Screenshot-2019-11-22-at-9.02.01-PM-100x70.png)


