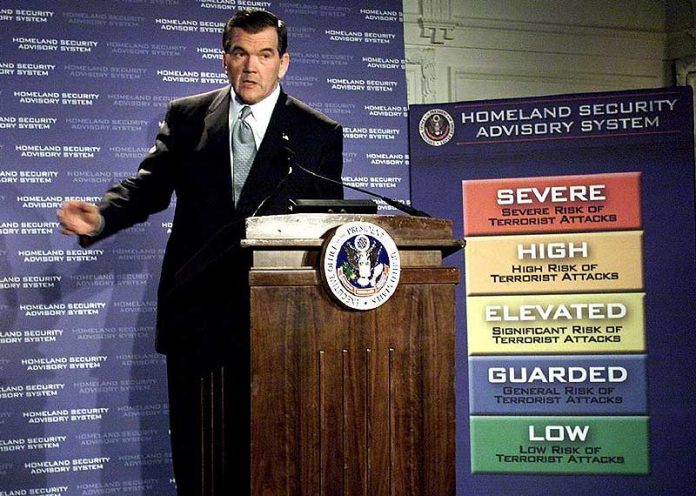
IARPA is furthering the police state. Due-process is dying, algorithms and technology will soon be judge, jury and executioner.
[fvplayer src=”https://player.vimeo.com/external/174208959.hd.mp4?s=08470f6c536a7b3ec6d724ba9af0649e5a2605dc&profile_id=119″ splash=”https://christianjournal.net/wp-content/uploads/2016/07/terror-alert-system.jpg”]
In the very near future, due-process will no longer be judge, jury, and executioner, but rather algorithms and technology will justify whether an individual is deemed an enemy of the state. IARPA, Intelligence Advanced Research Projects Activity, is seeking proposals in four technical categories: anticipatory intelligence, analysis, operations, and collection. With the latest advancements in cloud technology, it is becoming ever more desired to have an anticipatory intelligence to help predict and better connect intelligence dots.
IARPA will employ user generated cloud data all across the world to gather information, and with that intelligence; an algorithm will make predictions based on the taxonomies “wrapped” into the data stored in the cloud.
IARPA is interested in predictive technologies in detection and forecasting of emergent phenomena, automated generation and maintenance of taxonomies analysis and forecasting of rare events, quantitative risk assessments of emerging dual-use technologies, causal inference from observational data, methods for assessing capability and intent to develop weapons of mass destruction and methods for assessing capability and intent to leverage cyber capabilities against U.S. critical infrastructure.
In the name of National Security, IARPA will continue to gather data, most likely via the NSA, and analyze it to predict events, phenomena, and so on. This technology is the beginning of thought crimes. For example if your data happens to have a taxonomy that sets the algorithms alarm off, then the algorithm will attempt to make a threat assessment, and dispatch units to further “assess” the situation.
Not only is the NSA gathering all data that crosses the Internet, phone, and other lines, but now they are selling it off to the highest bidder. Following the Pentagon’s lead, The National Security Agency is turning to commercial vendors for layered cyber defense. So now not only will the government be analyzing all data, but so will the private sector. The commercialization of the United States government showcases the fact that American citizens are nothing but dollar signs to those who profit off the common man’s back.
The NSA cyber initiative also addresses criticism that federal agencies have been slow to address network vulnerabilities in the aftermath of a massive security breach last year at the Office of Personnel Management. In seeking commercial solutions for a proposed layered defense, NSA’s Information Assurance Directorate said the goals of CSfC include “developing new ways to leverage emerging technologies to deliver more timely [information assurance] solutions for rapidly evolving customer requirements.”
According to the program’s website, product requirements are in place for virtual private networks, campus wireless LANs, “data at rest” solutions and mobile access. Project managers added they would continue to use equipment supplied by government contractors as well as commercial products to protect classified information. However, the new directive adds that NSA’s Information Assurance Directorate (IAD) would “look first to commercial technology and commercial solutions in helping customers meet their needs for protecting classified information….”
The NSA and IARPA both seek better future predicting technology. However, this is not the only avenue from which the government is capturing data. Recently, IARPA announced that through the use of multiple cameras, different live feed sources, personal cameras, and so on that they plan to acquire better facial recognition software as well. The software would decipher patterns, and be able to assess suspicious behavior on live video.
In addition to the latest tyrannical invasion of privacy, kiss spoofing the facial recognition cameras and fingerprint scanners goodbye as well. IARPA is developing better technology that can detect when an individual is attempting to fool the biometric tracking systems.
The program, called “Thor,” aims to stop the so-called presentation attacks that make it difficult for biometric databases to correctly identify subjects. This might involve using a prosthetic to either hide the subject’s real prints, or to present someone else’s, a new IARPA announcement says.
Fingerprint mutilation and facial plastic surgery may also throw off current systems. A subject may also simply try to scan different parts of their finger on a sensor “to minimize overlapping data.”
As biometrics are increasingly important when determining someone’s identity, it’s key the identification systems “cannot easily be deceived” using a presentation attack. If detected, evaders could be prevented from passing through travel checkpoints, gaining access to secured facilities and being authenticated in cyber systems, according to IARPA.
All in the name of national security the police state is furthering its agenda into the minds of American citizens, and very soon through embedded technology; metadata captured in the cloud will be a thing of the past because governmental agencies will analyze the metadata of your mind.
SOUND OFF IN THE COMMENTS BELOW!
Works Cited
Mark Pomerleau. “IARPA wants intel tools that can predict the future.” Defense Systems. . (2016): . . https://defensesystems.com/articles/2016/07/06/iarpa-anticipatory-intelligence-algorithms.aspx
George Leopold. “NSA goes commercial to harden networks.” Defense Systems. . (2016): . . https://defensesystems.com/articles/2016/07/08/nsa-commercial-tech-network-security.aspx
Aliya Sternstein. “US Spies Are Building Software to Spot Your Suspicious Behavior In Live Video.” Defense One. . (2016): . . http://www.defenseone.com/technology/2016/06/new-us-spy-software-could-soon-spot-your-suspicious-behavior-live-video/128852/
NextGov. “IARPA Wants To Stop You From Spoofing Facial Scans and Fingerprints.” NextGov. . (2016): . . http://www.nextgov.com/cybersecurity/2016/06/iarpa-wants-stop-you-spoofing-facial-scans-and-fingerprints/129233/



![[VIDEO] Drag Queen Drag Shows Are Now Infesting Churches](https://christianjournal.net/wp-content/uploads/2019/11/Screenshot-2019-11-22-at-9.02.01-PM-100x70.png)
![[VIDEO] Starbucks Worker Dumps Milkshake On Open Air Preachers Head](https://christianjournal.net/wp-content/uploads/2019/11/Screenshot-2019-11-22-at-7.23.43-PM-100x70.png)
![[VIDEO] Man Arrested For Threatening To Kill Female Abolitionist With Crowbar](https://christianjournal.net/wp-content/uploads/2019/11/MLock-1-100x70.jpg)


